PowerShell and live response – why are they so good together?
 17.01.2022
17.01.2022
Healthcare under attack – Cyber security incident response in times of pandemic
 29.01.2021
29.01.2021
Cyber Kill Chain Based Approach for Intrusion Detection
 29.10.2020
29.10.2020
CISS2020-OL: Attacking the Secure Water Treatment testbed
 13.08.2020
13.08.2020
Adding Realism to Cyber Security Exercises – Populating RGCE environment
 11.06.2020
11.06.2020
Continuous integration in collaborative analysis of incidents = CINCAN
 05.06.2020
05.06.2020
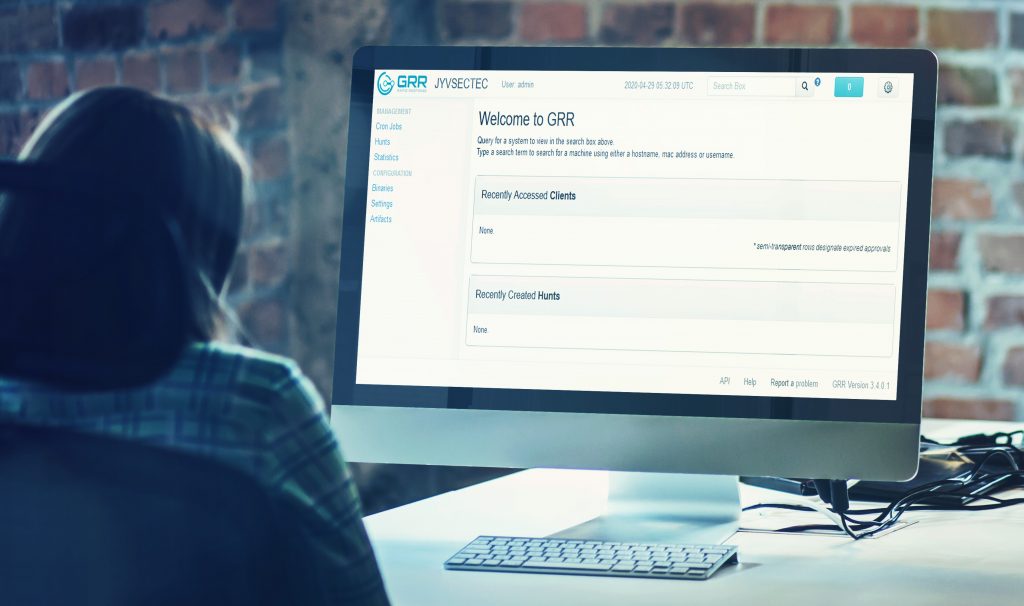
Carry out investigations remotely using containerized GRR
 14.05.2020
14.05.2020
Deploy the containerized GRR to unmask the intruders
 01.04.2020
01.04.2020
Police and organisations join forces in the control of cybercrime
 18.03.2020
18.03.2020
Experiences with Hardened Firefox
 21.02.2020
21.02.2020
Why are we sensitive to cyber attack
 26.11.2019
26.11.2019
Tool for extracting possible IoC information from files
 25.10.2019
25.10.2019
National Cyber Security Exercise 2019 is over or is it?
 12.06.2019
12.06.2019
Optimising and securing Dockerfiles
 26.04.2019
26.04.2019
Disobey – The Nordic Security Event
 13.03.2019
13.03.2019
Analysing malicious PDF documents using Dockerized tools
 01.02.2019
01.02.2019
From trainee to employee
 14.12.2018
14.12.2018
User Tracking in Internet
 14.11.2018
14.11.2018
RGCE organizational environments
 16.01.2018
16.01.2018
Experiences of the ECSO WG4 (SME group) meeting
 08.03.2017
08.03.2017
JYVSECTEC success story
 13.02.2017
13.02.2017
Cyber exercising to enhance performance
 15.12.2016
15.12.2016
Christmas greetings
 15.12.2015
15.12.2015
Cyber Challenge 2015
 30.11.2015
30.11.2015
Cyber security & ICT 2015 exhibition: Ready, Steady, Go!
 16.09.2015
16.09.2015