
The number of intrusions into organization IT environments has been increasing over the years. Detecting intrusions remains a difficult task as the long average adversary dwell times indicate (56 days in 2019, according to the FireEye M-Trends 2020 report).
A new approach for intrusion detection is to use a cyber kill chain-based model, where system events are mapped into well-known adversary techniques and tactic categories. After the event to adversary technique associations has been identified, data analysis methods can be applied to connect the events together to form the intrusion kill chain.
This blog post provides an overview of the intrusion kill chain and how it can be used for intrusion detection and investigation.
Intrusion Kill Chain
Kill chain is a systematic process to target and engage an adversary to create desired effects. This process is described as a “chain” because any single deficiency will interrupt the entire process. Originating from the military sector, Lockheed Martin has adopted the concept to information security as the Intrusion Kill Chain. The intrusion kill chain consists of multiple phases, which describe an adversary’s tactical objectives during operations, such as persist, discover targets or move laterally. The phases can be further divided into techniques, which are offensive actions that the adversaries use to accomplish the objectives, such as scripting, brute force or file deletion.
Forming the Kill Chain
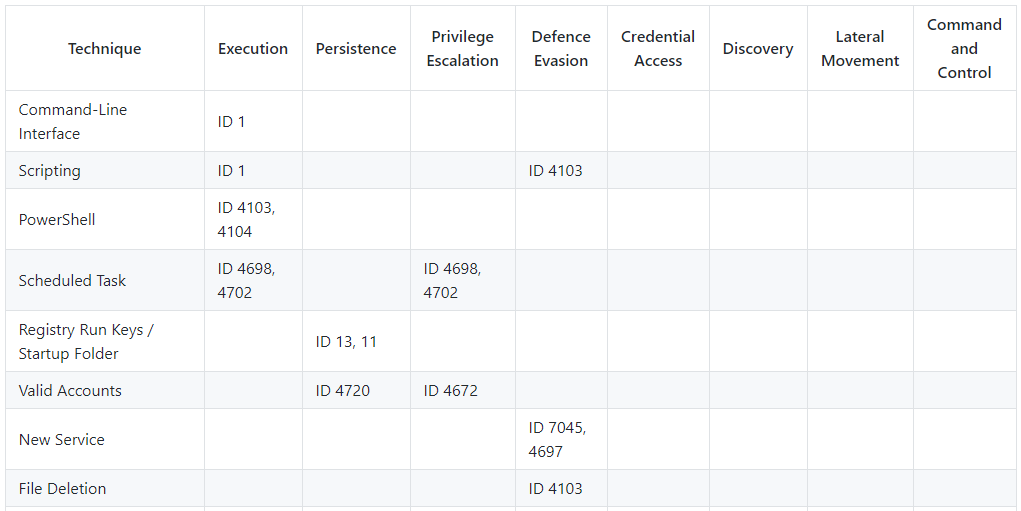
The First step for forming the intrusion kill chain is to identify the events related to adversary techniques. A good starting point is the JYVSECTEC PHR-model data collection section contains mappings of Windows Event ID to common adversary techniques (Figure 1). Another great resource is the MITRE ATT&CK knowledge base, which contains lots of information about adversary tactics, techniques, tools and data sources. After the events have been identified, they have to be mapped into techniques. This can be done either in the event collection or processing stage using tools such as Logstash.
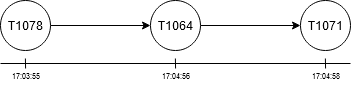
The next step is to connect events together by forming a graph. Graph consists of nodes and edges, which link nodes together. Individual events form nodes of the graph and edges can be formed by linking events together by some common field value, such as user name or IP address. In order to form a coherent chain of intrusion phases, the graph must be further transformed into directed graph by comparing connected node (event) timestamps and setting the direction from an older to a newer event (Figure 2).
A graph of a kill chain is not in itself hugely valuable without a visual representation. A proper visualization of the graph helps identifying the order of events, highlights anomalies and allows users to get more details about the events and the context in which they occur.
Conclusions
Identifying the intrusion kill chain can enable faster detection of the intrusion, help with establishing the source of events as well as identify the adversary group and its motive. It is important to consider organization/environment specific variables when mapping events to adversary techniques in order to avoid false positives. Selecting the right fields for connecting events together is also crucial, as it affects coverage of the resulting graph of the kill chain.
Want to read more about how cyber kill chain can be utilized for intrusion detection? I cover the topic in depth with a proof of concept technical implementation in my Master’s Thesis Event-driven Analysis of Cyber Kill Chain, which was conducted as part of the JAMK University of Applied Sciences CYBERDI project.
 |
Jani Hallberg Systems and Network Administrator JAMK University of Applied Sciences, The Institute of Information Technology |



