Some say all good things must come to an end. The CINCAN project started in 2018 and this 2-year project, co-financed by the Connecting Europe Facility of the European Union, is reaching the end on June 2020. The project was established with a mission to make the jobs of national cyber security operators easier by creating open source tools and automated tool chains using the methods of software development, the focus being on malware analysis, threat detection and threat intelligence handling.
Getting started
In the beginning of the project, we started by gathering information on the most widely used DFIR (digital forensics/incident response) tools, mostly open source ones, and began containerizing and testing them. The dockerizing of tools takes out the “works on my machine” effect. If you just have Docker installed, the tools work the same way basically on every machine, removing the inconvenience of installing all the different tools, and the possible settling of version problems.
In addition to just running dockerized DFIR tools on their own, we have tested them also as parts of continuous integration (CI) pipelines, and built several analysis pipelines upon the Concourse CI, and our own command line tools.
Key achievements
DFIR tools
So, what have we accomplished? At the time of writing, we have about 80 tools to run with Docker command (or rather with the cincan tool, we’ll come to that later), all containerized using the best practice guidelines, which were created during the project. These guidelines, with automated testing, ensure that the tools are containerized the right way, and are up to date. Many tools have thousands of downloads from the Docker hub already.
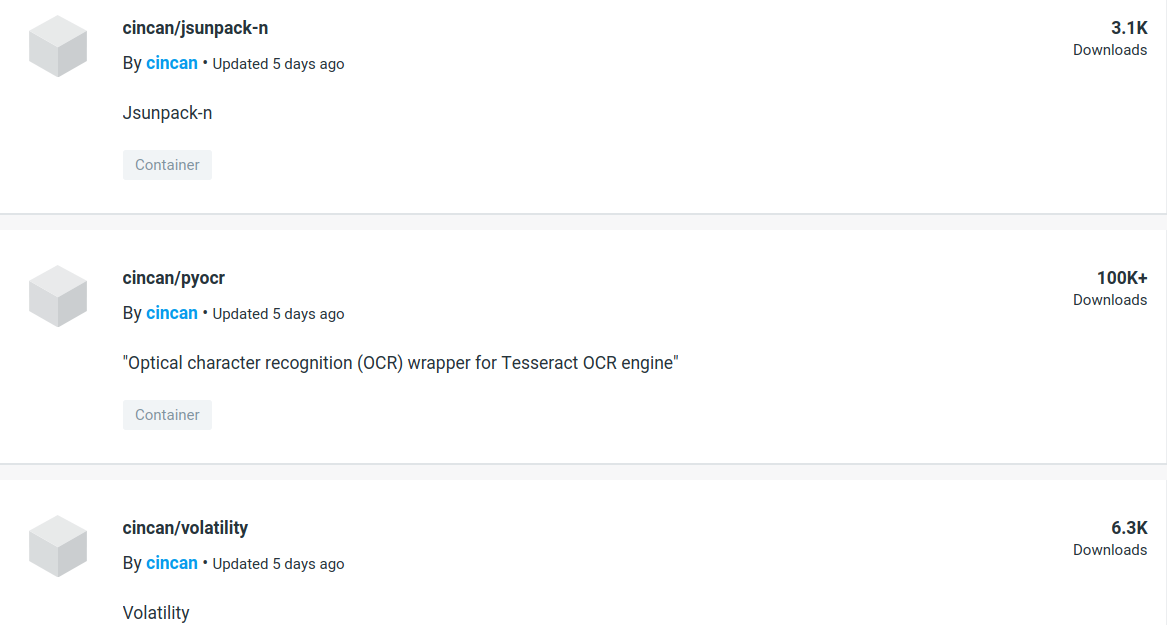
Some tools at hub.docker.com/u/cincan
Cincan command line tool
The cincan tool makes it easier to run the dockerized tools. You can use cincan the same way as docker, but without the need of mounting volumes. The input and output files are automatically passed.
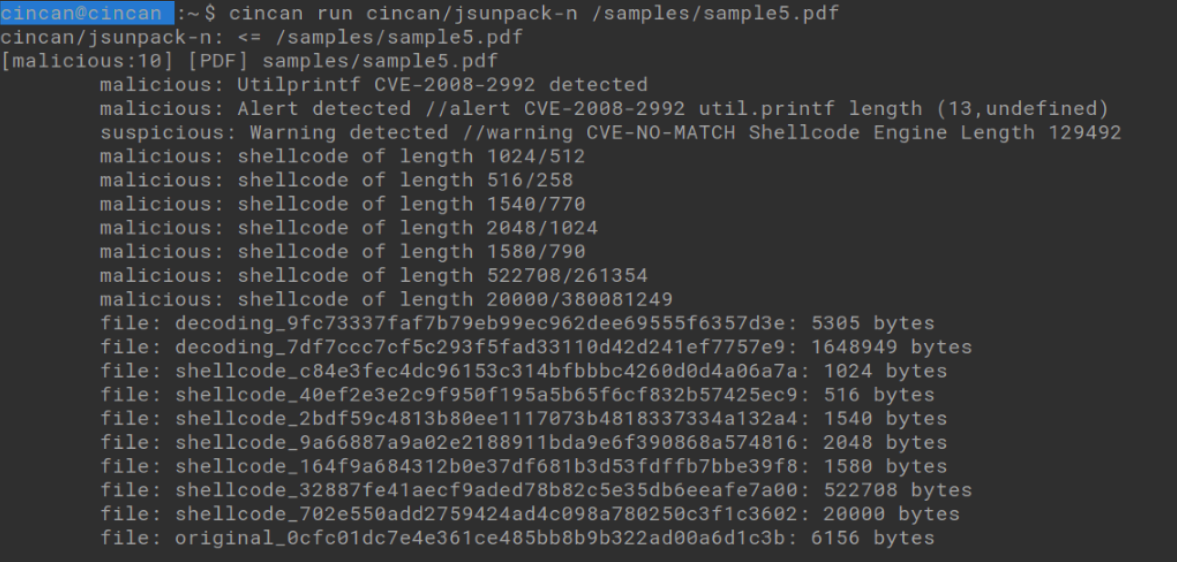
Running cincan/jsunpack-n with the cincan-command.
As an extra help in choosing the right tools for a job, all CINCAN tools, that are available in the Docker hub, can be listed with the command cincan list.
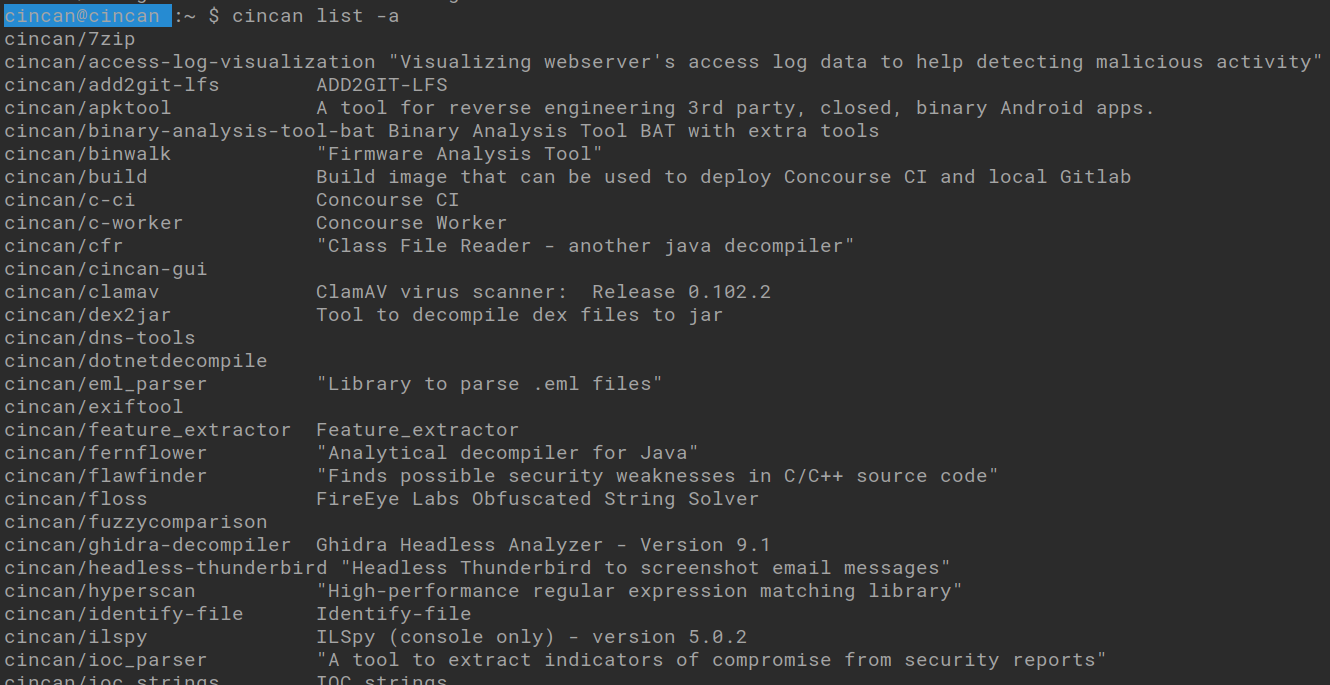
Part of “cincan list” output.
Minion
Minion is a tool for building analysis pipelines in command line. It can run a set of dockerized tools based on rule files. For example, if you are going to analyze a PDF, you can command minion to apply PDF rules for the file, and then it analyzes the sample with tools like strings, pdfid, jsunpack-n and clam-av. As the analysis is complete, the results from all the tools can be examined in designated folders. You can also easily create your own minion rules, to automate your workflow, as told in this earlier blog post Automating your .apk reverse engineering workflow.
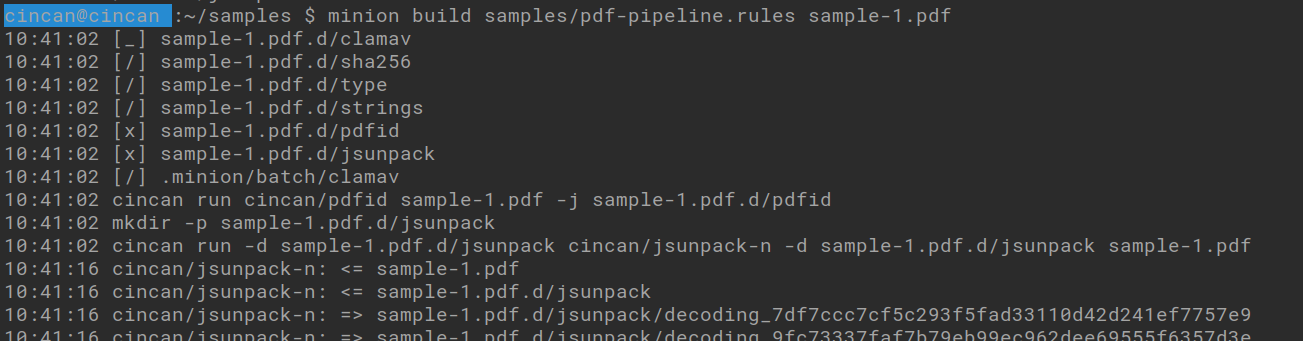
Minion running clamav, sha256, type, strings, pdfid, jsunpack-n and clamav for a PDF file.
Concourse pipelines
During the project, we have created several pipelines for the Concourse CI, the most complete one being a document analysis pipeline which can be used to analyze PDF and MS Office files. Some other available pipelines include analyzing PE, PCAP and emails, for example. We have also created a pilot environment that sets up the Concourse CI with local Gitlab on Docker containers. The environment is easy to setup, and some pipelines include a quick setup script as well, making a low effort pipeline testing possible.
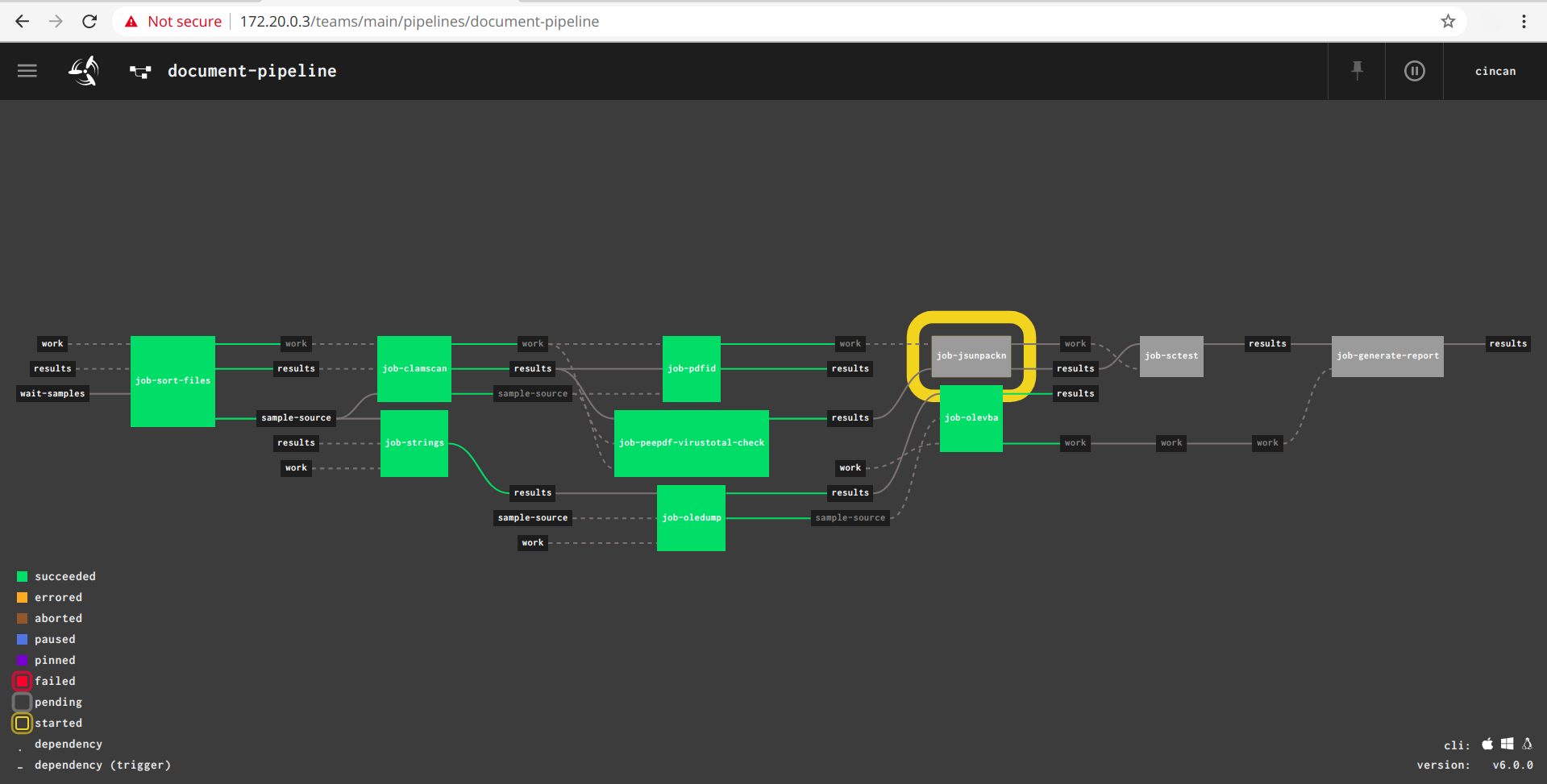
The document-pipeline combines results from several PDF analysis tools and OLE-tools into a comprehensive report that can be viewed in a browser window.
Threat intelligence feeds
One minor research area has been to evaluate the quality of threat intelligence feeds, to help analysts to decide the relevance of IOCs (indicators of compromise). We have created some tools to help on this area, tools that can show dynamicity and timeliness of the feeds and run Cortex-analyzers resulting in a configurable HTML report. You can read more about this in an earlier blog post Investigating IoCs in malware using cincan command.
The end is near, or is it?
One last thing. This good that the CinCan project has started, does not have to end after all! With your help, along with other enthusiasts, these tools can live on. You can contribute at gitlab.com/CinCan, and help in developing this great set of open source DFIR tools and tool chains furthermore!
 |
Vesa Vertainen
Project Engineer |